eDiscovery in the light of AI: What's in store for you?
AI in eDiscovery is revolutionizing legal reviews by accelerating workflows, ensuring compliance, reducing risks, and transforming legal operations.
Learn how CIOs can accelerate digital transformation through cloud modernization, from security-by-design and policy-as-code to measurable business outcomes and compliance automation.

Any CIO who has sat through a post-breach board presentation understands that cloud security is not a feature to be added eventually after a breach takes place. It is the foundation on which everything else operates. And yet, security remains one of the most frequently deferred priorities in enterprise cloud modernization programs, because the short-term pressure to deliver product velocity consistently outweighs the longer-term risk associated with cloud architecture.
Cloud environments that grow through rapid, ungoverned migration accumulate risk in the gaps that might come up between tools, teams, and accountability. Misconfigurations, over-permissioned service accounts, or maybe inconsistent patch management across accounts are not theoretical risks. They are common findings in cloud security assessments at organizations of every size, across every sector, and at every stage of cloud maturity.
Cloud security is how a well-architected cloud environment is designed from day one. The practices that define a security-by-design cloud modernization are also the practices that directly show how Cloud Automation and DevSecOps culture can transform your team from being busy to being more strategic.
The practices that define a security-by-design cloud modernization are also the practices that directly show how Cloud Automation can transform your team from being busy to being more strategic.
Policy-as-code: Security guardrails are defined in version-controlled code and reviewed with your application. They are enforced automatically so that developers cannot deploy unencrypted, public storage buckets.
Consistent Infrastructure: Environments are rebuilt from a verified baseline at every deployment instead of being patched over time. This process eliminates configuration drift and removes the undocumented changes that make systems unpredictable or hard to audit.
Zero Trust Architecture: Service accounts and access rights are limited to the exact permissions required for a specific duration. Least-privilege access is the default setting. This approach reduces the potential impact of any compromised credentials.
Automated Compliance: Compliance controls are validated continuously within the delivery pipeline instead of during manual quarterly audits. This ensures that security evidence is always current rather than weeks out of date by the time reviewers see it.
Unified Cloud Observability: A single view across all accounts and regions allows security teams to detect anomalies in real time. Teams can respond to live threats immediately instead of trying to reconstruct events from disconnected logs after an incident.
Let’s say a healthcare technology company, operating across multiple geographies, is preparing for a SOC 2 Type II audit. As per their legacy processes, gathering audit evidence required three weeks of engineering time and four weeks of back-and-forth with external auditors. Controls existed in documentation but had not been consistently enforced in practice. Hence, this resulted in findings that required an update before the audit could close.
After modernizing with policy-as-code and automated compliance reporting, the same audit evidence gets generated in 48 hours. Controls are enforced continuously and documented automatically across every environment. The CISO presented this to the board as a major risk reduction milestone. Continuous compliance means the organization is audit-ready on any given day. Eventually this gets noticed by regulators as well as enterprise clients whose procurement processes include security due diligence.
Technology decisions are not made in isolation by the people responsible for executing them. One of the most consistently underestimated risks in cloud modernization programs is the organizational change dimension.
Implying, the engineers who have spent years mastering the legacy systems being replaced, the operations teams whose workflows are built entirely around processes that modernization will disrupt, and the technical leadership layer that may feel threatened by a shift toward automated operations and platform engineering.
It is a program delivery risk that has derailed modernization initiatives at organizations with sound technology choices, adequate funding, and strong executive sponsorship. The result being, the architecture was right, but the change management was not.
Investing in upskilling and giving engineers ownership over new standards creates sustainable momentum. The people who know the legacy system's failure modes are also best positioned to ensure the new system does not inherit them.
Cloud modernization that does not account for organizational change management will consistently underperform its technical potential. The CIO's role does not end with selecting the right cloud-native architecture. CIO’s role is to give the people executing the work a compelling reason to build it well.
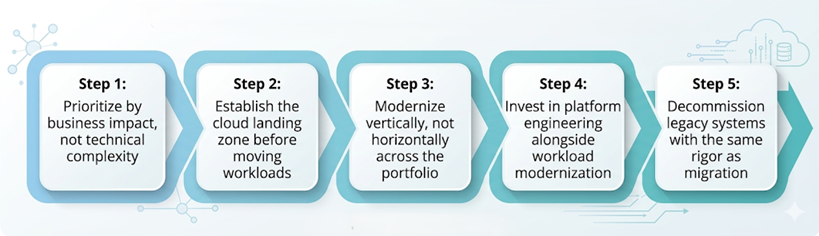
The cloud transformation roadmap that tends to survive organizational pressure is structured around business value milestones rather than technical delivery phases. Each stage should produce something the business can see, measure, and identify as evidence that shows value.
What the roadmap looks like:
Executives often lose interest in cloud modernization because engineering metrics fail to translate to business value. While deployment frequency and recovery times matter to operations, they do not show the CFO how the infrastructure investment improved the company's bottom line.
CIOs who build sustained sponsorship connect their cloud modernization KPIs directly to business outcomes that non-technical leaders recognize and care about.
Time from Requirement to Deployment: This metric directly measures organizational agility in a way any business leader understands. When this speed increases, the entire business feels the impact.
Automated Compliance Evidence: This percentage measures both the maturity of your security posture and the engineering hours saved from manual audit work. It tracks how much time is recovered for productive tasks each quarter.
Customer-Impacting Incidents:: Linking infrastructure failures to customer incidents connects technical reliability to revenue and trust. This allows boards to track cloud health as a business continuity risk. .
Recaptured Engineering Capacity: Redirecting engineering time from maintenance to product development turns platform investment into business terms. This helps a CFO evaluate headcount decisions and build-versus-buy scenarios.
Misconfiguration Incidents: Tracking security incidents caused by misconfiguration shows the progress of your security-by-design strategy. A steady decline in this metric provides concrete evidence that the architecture is working.
Gartner projects global end-user spending on public cloud services will exceed $1 trillion by 2027. The organizations that capture disproportionate value from that investment will not be the ones that spent the most. They will be the ones that measured the right things and modernized with the clearest connection to business outcomes.
Legacy IT infrastructure does not hold its position for free. It requires ongoing maintenance investment, accumulates technical debt at a rate that accelerates over time, and makes it harder for the company to use new tools.
Every year that cloud modernization is delayed is a year in which the architectural gap between your operating environment and your competitors widens. And the gap rarely stays constant. Once a competitor has modernized and achieved continuous delivery, their ability to respond to market changes, regulatory shifts, and customer feedback enhances.
The CIOs who are most effective in this environment are not necessarily those with the largest modernization budgets. They are the ones who can articulate the cost of inaction as precisely as the cost of action, changing the board's conversation from "can we afford to modernize?" to "can we afford not to?"
The CIOs who are most effective in this environment are not necessarily those with the largest modernization budgets. They are the ones who can articulate the cost of inaction as precisely as the cost of action. This narrative changes the board’s conversation from ‘can we afford to modernize?’ to ‘can we afford not to?’
Cloud modernization is not a destination. It is the operating model that determines whether your organization keeps pace with the market or falls behind it. For a CIO carrying the dual mandate of protecting the business today and accelerating it tomorrow, that is where the work is concentrated.
Schedule a call with our team today to understand your business and the market dynamics with Cloud Modernization strategy.
Cloud modernization is the process of migrating, re-architecting, and operating enterprise systems on cloud infrastructure using practices such as infrastructure-as-code, policy-as-code, zero trust security, and automated compliance. For CIOs, it matters because legacy infrastructure accumulates technical debt, widens the architectural gap versus competitors, and makes it harder to adopt AI and respond to market changes at speed.
Policy-as-code means defining and enforcing security guardrails through version-controlled code that is reviewed alongside application code and applied automatically at deployment. It prevents insecure configurations, such as unencrypted or publicly accessible storage buckets, from ever reaching production, without requiring manual review at every stage.
Zero trust architecture limits service accounts and access rights to the exact permissions required for a specific task and duration, making least-privilege access the default. This reduces the potential blast radius of any compromised credential because no account holds standing permissions beyond what it immediately needs.
The most board-relevant KPIs include: time from requirement to deployment (organizational agility), percentage of compliance evidence generated automatically (security maturity and hours saved), number of customer-impacting incidents (reliability as a business continuity metric), recaptured engineering capacity (platform investment in business terms), and reduction in misconfiguration-related security incidents (security-by-design progress).
Delaying cloud modernization is not a neutral decision. Legacy infrastructure requires ongoing maintenance investment, accumulates technical debt at an accelerating rate, and limits the organization's ability to adopt new tools. Each year of delay widens the competitive gap with peers who have achieved continuous delivery, faster regulatory response, and lower infrastructure costs per unit of output.
AI in eDiscovery is revolutionizing legal reviews by accelerating workflows, ensuring compliance, reducing risks, and transforming legal operations.
Explore how AI enhances eDiscovery with predictive coding, smart review, and automation—speeding legal workflows while cutting costs and boosting...
Move beyond AI pilots. Discover a 6-phase enterprise AI roadmap focusing on data activation, agentic workflows, and measurable ROI for business...
Be the first to know about new B2B SaaS Marketing insights to build or refine your marketing function with the tools and knowledge of today’s industry.